Zero Trust
-

Sea-Air-Space: Zero Trust is ‘The Best Approach’ For Military Cybersecurity
10m watch -

How Agencies are Justifying Budget Growth in AI, Zero Trust
3m read
How TMF is Helping Agencies Accelerate Tech Modernization
The program launched a new AI pilot to expedite TMF applications as agency leaders urge more to consider applying for funds.

This is a carousel with manually rotating slides. Use Next and Previous buttons to navigate or jump to a slide with the slide dots
-

DOJ Weighs 'Bring Your Own Devices' Amid Increased Threats
The agency wants stronger industry standards around cybersecurity before considering a more tailored mobile device policy.
2m read -
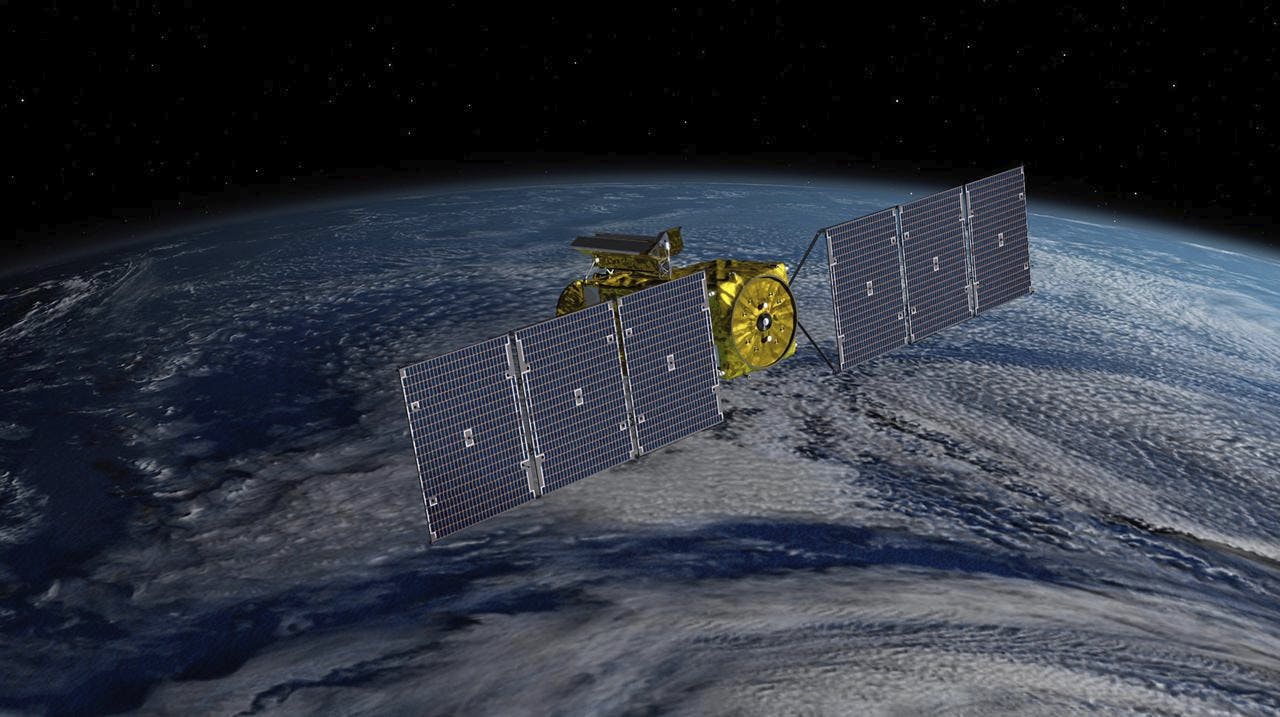
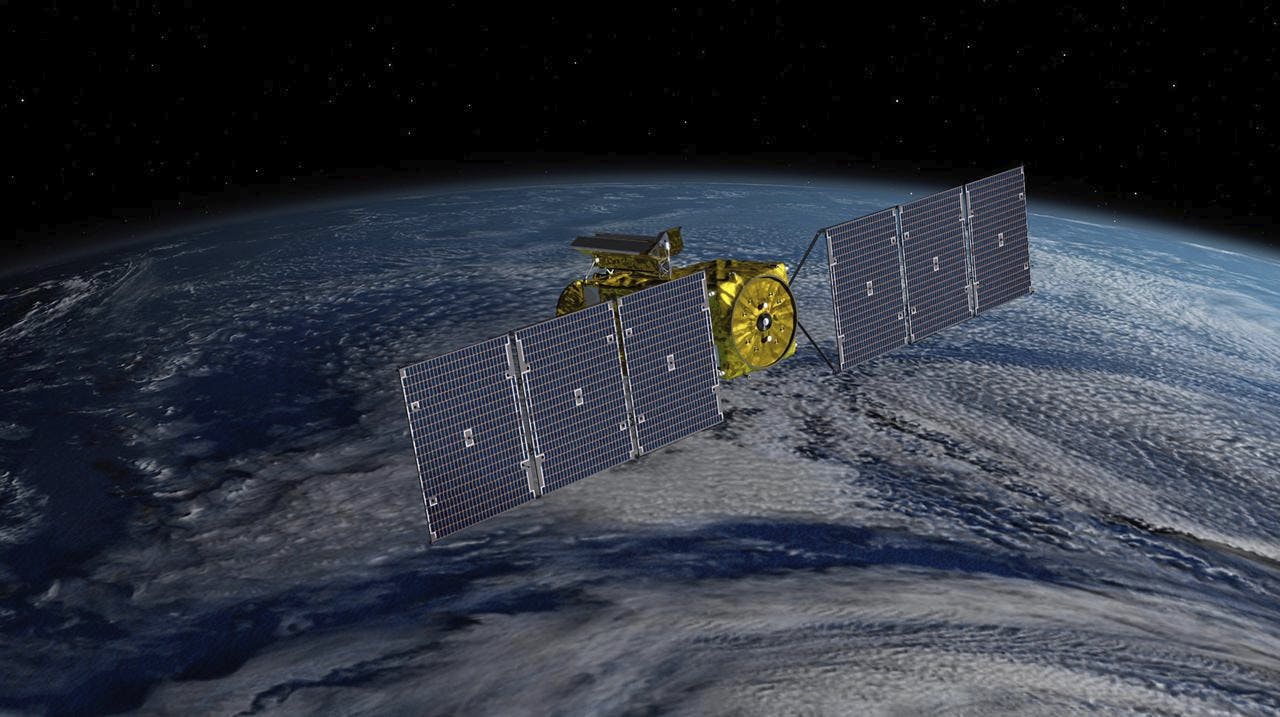
Officials Consider Zero Trust Challenges for Satellite Cybersecurity
Infrastructure experts call for better public-private cooperation to tackle cybersecurity in the planet's orbit.
4m read -
CISA, DOD Tackle Next Steps in Zero-Trust Implementation
Federal leaders discuss future strategies and culture impacts around successful zero trust implementation amid new organizational structures.
3m read -

Federal National Cyber Strategy 2.0 on the Way
As agency leaders and industry partners work to implement the plan, working across organizations is critical to strengthening cyber defenses.
5m read

Zero Trust Enabling the Future Joint Force
This Navy's Director of Enterprise Networks and Cybersecurity, Scott St. Pierre, and Fortinet Federal VP Mark Wiggins explore how zero trust aids secure communication and data sharing to prepare the Navy for future fights.
Watch Now- Scott St. Pierre Director Enterprise Networks and Cybersecurity (OPNAC N2N6D), US Navy
- Mark Wiggins VP, Defense, Intelligence Community and System Integrators, Fortinet Federal
Protecting the Health Care Ecosystem from Cybersecurity Threats
Brian Mazanec will use his expertise in cybersecurity and conflict to ensure the health care ecosystem has critical infrastructure protection to combat cyber threats.
Listen Now
-

Cyber Resilience and Recovery Amid Evolving Cyber Threats
Data durability is a key aspect of NIST’s cybersecurity framework for public and private organizations.
21m listen -

How Tech Enables Environmental Justice at EPA
The agency wants to eliminate bias and establish new tech standards to reduce greenhouse gas emissions.
39m listen -

Building Better Data Governance Across FDA
The agency is using emerging technology to tackle its data challenges.
19m listen -

Coast Guard Poised for Growth in Cyber
The service’s prevention policy chief discusses his priorities for combatting cyber incidents that could have global impacts.
23m listen