Why a Common Language is Key to Zero Trust
Both NASA and FDIC say government needs to facilitate common language for communication that results in action.
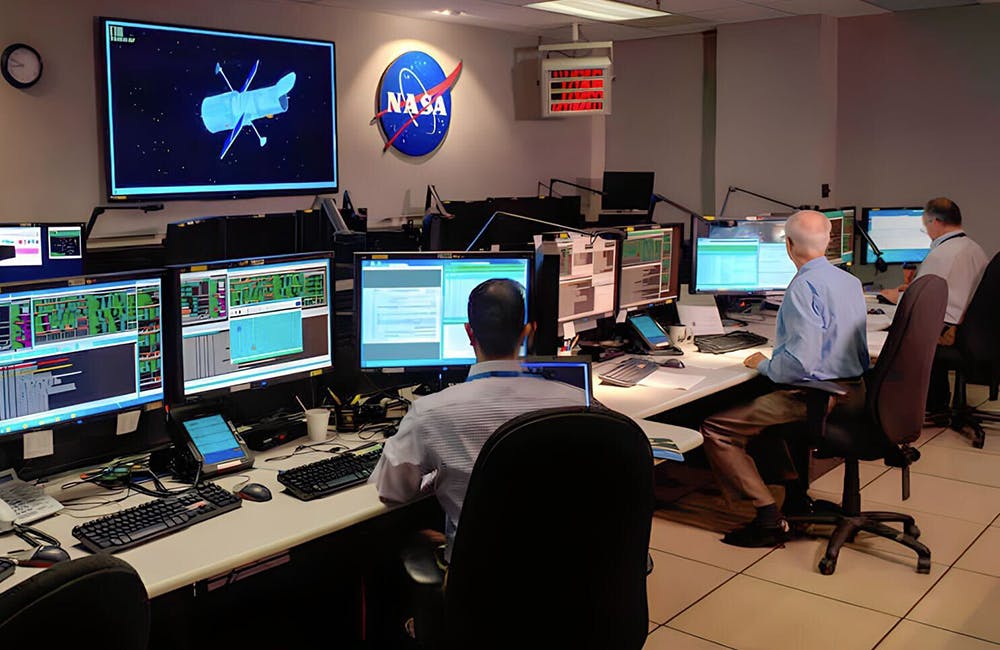
NASA is currently in the process of decomposing the 19 actions listed in the White House’s zero trust memo, according to Karim Said, CIO for the office of strategic infrastructure. For Said, one of his key strategies for implementing zero trust is lowering communication barriers within the agency.
“There are so many different groups within our large enterprises that are responsible for some portion of zero trust, and barriers to communication between those groups is probably our biggest challenge,” he said at ATARC’s Zero Trust summit last week. “So at NASA, one of the big things I’m doing is being the loud person advocating for the adoption of modern, open-source software development concepts — not just for writing code, but also for developing the policy that governs our IT.”
For Stephen Haselhorst, zero trust program manager at the Federal Deposit Insurance Corporation (FDIC), White House directives like the cybersecurity executive order and accompanying memo have helped light a fire under zero trust efforts. FDIC has decomposed the tasks identified in the memo and added some tasks of their own.
“I really welcome the direction and the guidance because when you’re trying to sell zero trust, and to the nonbelievers and whatnot, it’s a little hard,” he said. “This legitimizes it. It makes it a lot easier for us who are trying to evangelize zero trust and push zero trust in an organization.”
Putting the principles of zero trust and the steps to get there in plain language is critical to making progress, Said said. Said has experience researching computer-supported cooperative work, and his zero trust strategy is informed by the findings of Wanda Orlikowski, Alfred P. Sloan professor of information technologies and organization studies at MIT’s Sloan School of Management.
“Thematic to all of her research is that any large enterprise, when it comes to technology adoption, the big dynamic variable there is not the technology — it’s the people and how much voice you give to the people who are contributing to the adoption,” he said. “Let’s think of all the different folks that are managing all these disparate parts of our IT infrastructure. How do they all communicate? Well, traditionally they don’t do it really well. As cybersecurity professionals, though, we have a thing that we can bring them all to the table with.”
But just bringing people to the table isn’t enough, Said said. You have to ensure that everyone has a common language to facilitate communication that results in action.
“If we can coalesce around a common language and communicate about risk consistently and efficiently across all these different groups, that’s really our best bet at coming up with any sort of plan to get something like zero trust in place,” he said. “And that’s why I think one of the most important things we’re currently working on as a cybersecurity community in the federal government is the development of common standards.”
This is a carousel with manually rotating slides. Use Next and Previous buttons to navigate or jump to a slide with the slide dots
-

Cyber Resilience and Recovery Amid Evolving Cyber Threats
Data durability is a key aspect of NIST’s cybersecurity framework for public and private organizations.
21m listen -

How TMF is Helping Agencies Accelerate Tech Modernization
The program launched a new AI pilot to expedite TMF applications as agency leaders urge more to consider applying for funds.
4m read -

Energy Researchers Aim For Holistic Approach to AI Issues
A new center at the Oak Ridge National Laboratory is looking at under-researched areas of AI to better understand how to secure it.
2m read -

A Prepared Workforce is Key to Cyber Resiliency
Strong training strategies and emphasizing cyber hygiene basics enhance security practices at federal agencies.
2m read








