Government Embarks on New Collaborative Approach to Cyber Threats
The newly announced joint cyber effort is the latest in a series of new initiatives aimed at securing agencies, with CISA leading that way.

CISA Director Jen Easterly announced her agency’s new Joint Cyber Defense Collaborative, or JCDC, at Black Hat earlier this month. The move signals a new era of cyber incident information-sharing and establishes CISA as the leader.
The new collaborative, stylized like the classic rock band AC/DC, aims to make cyber information-sharing “cool” in a cyber environment where federal agencies and industry partners do not always share important cyber threat and incident information with CISA in a timely manner.
Along with jokes and references to the show Seinfeld, Easterly’s announcement also stressed the importance of imagination over knowledge. Imagination, she said, will enable cyber defenders to dream up fresh solutions to the multitude of cyber problems facing the U.S.
“We’re at an incredible moment in time where an administration has made cybersecurity a national security imperative,” she said. “CISA was created to be something very different — something much more akin to a public-private collaborative. Collaboration is baked into our DNA.”
The JCDC, she added, is all about collaboration between federal agencies and industry. The initial group of JCDC partners include the Defense Department, the FBI, the National Security Agency, U.S. Cyber Command, Amazon, Google, CrowdStrike, Lumen, Microsoft and others. The two initial focus areas are in combatting ransomware and “developing a planning framework to respond to incidents with cloud providers,” Easterly said.
“You’ve got to plan in peacetime so you’re ready in wartime,” she said. “[JCDC will do] four key things: share insight so we create a common operating pic and shared awareness of the threat environment, develop whole-of-nation cyber defense plans to deal with the most significant threats to the nation’s critical infrastructure, exercise these plans, and finally work together to implement these cyber defense plans into actual operations and make sure we can do that to reduce risk to the nation. Some of these activities are already going on across the federal government, but they’re happening largely in stovepipes.”
Protecting federal agencies like the FDA, Transportation Security Administration, and the departments of Veterans Affairs, Health and Human Services, and Transportation is a No. 1 priority for JCDC, she added.
Easterly’s emphasis on collaboration and information-sharing is the drumbeat anchoring the recent chorus of cyber initiatives and perspectives voiced by Congress, the White House and other federal agencies.
Earlier this month, three senators introduced the Defense of the United States Infrastructure Act, which would create a Bureau of Cyber Statistics within the Department of Homeland Security to track cyber threat and vulnerability trends.
Plus, National Cyber Director Chris Inglis said a Bureau of Cyber Statistics would help federal cyber defenders gain a more holistic and informed view of the state of cybersecurity at an Atlantic Council event last week.
Speaking at an FCW Cybersecurity Workshop this week, Federal CISO Chris DeRusha echoed Easterly’s information-sharing priorities and said zero trust architectures will be key to improving federal cybersecurity.
“From where I sit it doesn’t look like (cyber incidents) are slowing down anytime soon. We cannot predict what the next incident will look like,” DeRusha said at the event. “We have the very hard challenge of being prepared for them all. We need a paradigm shift in cybersecurity, and for us, that means moving to zero trust principles. We’re talking about re-architecting our network access so that everyone and everything is untrustworthy until proven otherwise.”
Chris Clearly, CISO at the Department of the Navy, described cybersecurity as an “infinite game” that requires more resources and communication. He challenged IT departments not to look at cyber investment as a budgetary fight.
“The people inside the cyber community, we all get it,” he said at the FCW event. “It’s us talking outside of our communities, bringing this story to the people who have no idea what this is and get them to appreciate our jobs (and that we’re not just trying to get more money for new tools or widgets).”
This is a carousel with manually rotating slides. Use Next and Previous buttons to navigate or jump to a slide with the slide dots
-

Sea-Air-Space: Zero Trust is ‘The Best Approach’ For Military Cybersecurity
Marines Cyber Technology Officer Shery Thomas discusses identity management across networks and devices.
10m watch -

How Agencies are Justifying Budget Growth in AI, Zero Trust
IT leaders stressed the importance of understanding user knowledge and needs when prioritizing cybersecurity projects.
3m read -

DOJ Weighs 'Bring Your Own Devices' Amid Increased Threats
The agency wants stronger industry standards around cybersecurity before considering a more tailored mobile device policy.
2m read -
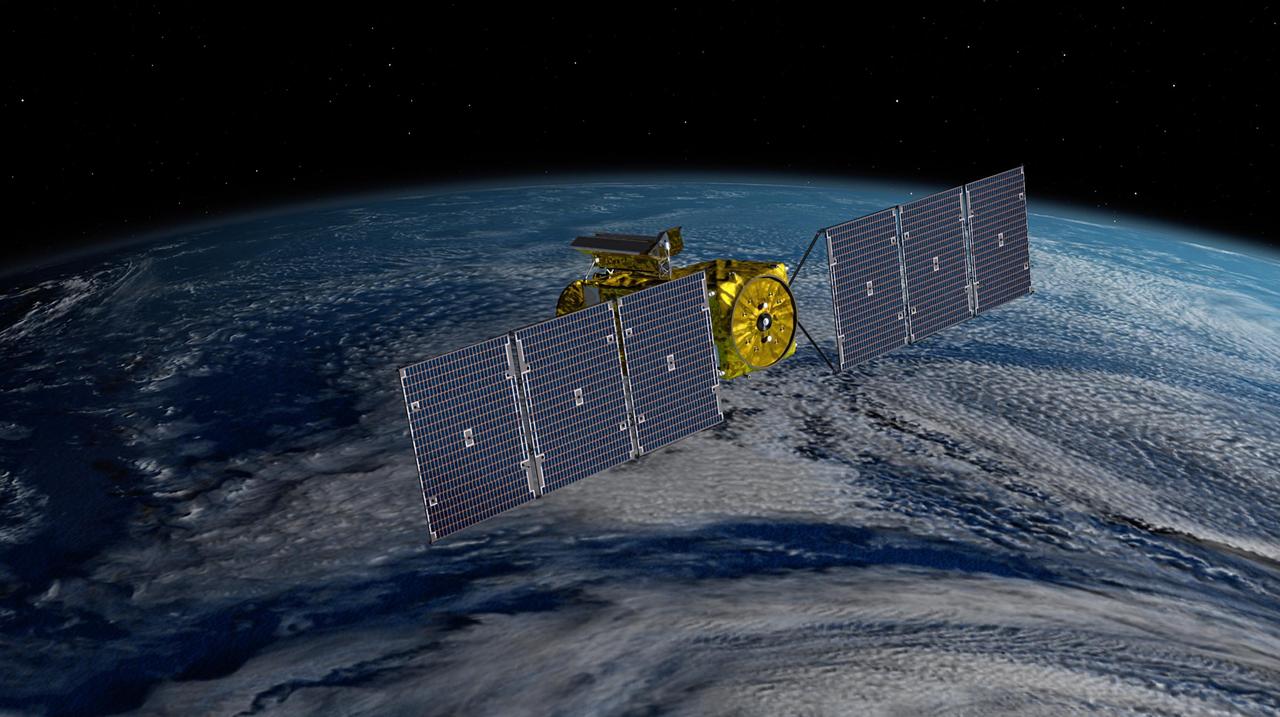
Officials Consider Zero Trust Challenges for Satellite Cybersecurity
Infrastructure experts call for better public-private cooperation to tackle cybersecurity in the planet's orbit.
4m read




