Feds Tackle Growing Ransomware Risks With Zero Trust
The commander of the U.S. Cyber Command and director of the National Security Agency (NSA), Gen. Paul Nakasone, declared ransomware a national security threat in 2021 following compromises to critical infrastructure and key resources. The SolarWinds and Colonial Pipeline attacks, along with virtual network expansions, have forced organizations to build a stronger cybersecurity infrastructure to better detect security risks.
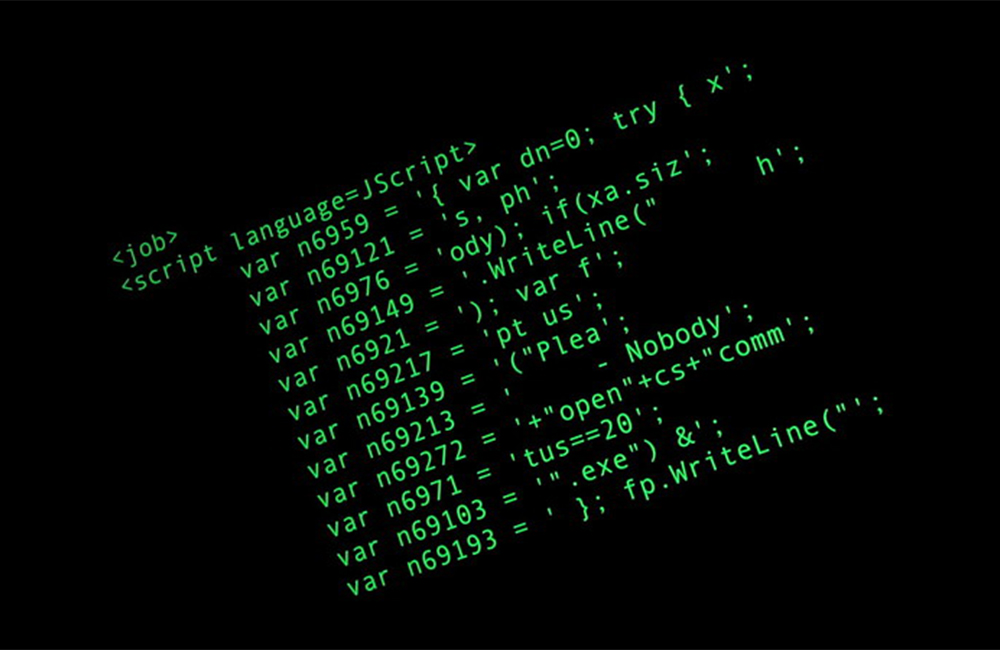
Recent progress in zero trust and privileged access management (PAM) solutions are helping combat these evolving ransomware threats, especially amid what’s called ransomware-as-a-service (RaaS), a subscription-based model that enables affiliates to use already-developed ransomware tools to execute their attacks. With these types of models, bad actors and adversaries do not have to be well versed in ransomware in order to use the tools for attacks.
This contributes to as much as a 200% rise in ransomware attacks in the past two years in the U.S., according to a 2021 report from Delinea.
The shift from “vertically oriented” threat actors, who make and then attack organizations using their own bespoke ransomware, to the RaaS model where one group builds the ransomware and then leases the use of that ransomware out to specialists has changed the threat landscape and increased scale and number of attacks.
In 2022 and beyond, the RaaS business model will continue to dominate the threat landscape for ransomware attacks, according to another report from Sophos. This model enables ransomware developers to continue to improve the attack vector and increase attack intensity, without slowing attacks.
“We’ve already seen these RaaS threat actors innovate new ways to break into progressively more well-defended networks, and we expect to see them continue to push in this direction in the year to come,” the Sophos report said.
As cyber threats become more prevalent and sophisticated, the Biden administration is directing agencies to improve defenses to prevent, disrupt or mitigate attacks. The White House Executive Order on Improving the Nation’s Cybersecurity takes a holistic approach to securing networks, requiring agencies to shift toward zero trust architectures and adopt advanced security solutions.
PAM solutions are key here. By enforcing “least privilege” principles, organizations can prevent credential harvesting and lateral movement, reducing attacker dwell time and making it more difficult to use ransomware tools. Plus, PAM policies enable security teams to identify the attack entry point, understand what’s happened, help remediate and ultimately protect restored data — the end goal of any zero trust approach.
“Least privilege is one of the many essential components of zero trust,” DLT Chief Cyber Security Technologist Don Maclean said during a GovFocus earlier this year. “All human systems and users only have the privilege they need to do their jobs. I’ve been involved in least privilege exercises, and what you find is, often, with the hurry to get things done, excessive privileges are given and you don’t want to sit there and parse out what they don’t need. Once people have privilege, they feel privileged and important. Rescinding those privileges becomes an exercise in human management and knowing what they actually need to do their jobs. That’s just one example of the types of cultural things that will be difficult in implementing a zero trust program.”
The NSA recently released guidance for embracing a zero trust approach, noting these “principles can better position [cybersecurity professionals] to secure sensitive data, systems, and services.”
NSA’s 2021 Cybersecurity Year in Review outlined how NSA worked to prevent and eradicate threats to critical systems over the past year. One of the agency’s top highlights was working with partners, through its Cybersecurity Collaboration Center, to respond to national-level threats, like SolarWinds and multiple ransomware attacks on U.S. critical infrastructure.
“While many of our mission successes must remain classified, I’m proud that we can showcase how NSA Cybersecurity helps contribute to securing the nation in this report,” said Rob Joyce, NSA’s cybersecurity director, according to a press release. “The successes really show the value NSA cybersecurity delivers through its foreign threat intelligence insights, partnerships and expertise.”
NSA worked collaboratively to analyze cyber threats and share insights through its foreign signals intelligence about the cyber criminals profiting from ransomware and their infrastructure. The agency alongside U.S. Cyber Command and other government and industry organizations pursued the actors, capabilities and finances driving global threats.
“Throughout the effort, NSA ensured that its threat intelligence was disseminated at the lowest possible classification level, so that it generated outcomes,” the report said.
This is a carousel with manually rotating slides. Use Next and Previous buttons to navigate or jump to a slide with the slide dots
-

Transitioning Systems for Modern Agency Missions
IT modernization is a constant process necessary for improving customer service, mission delivery and collaboration.
40m watch -

Cyber Resilience and Recovery Amid Evolving Cyber Threats
Data durability is a key aspect of NIST’s cybersecurity framework for public and private organizations.
21m listen -

How Tech Enables Environmental Justice at EPA
The agency wants to eliminate bias and establish new tech standards to reduce greenhouse gas emissions.
39m listen -

The CAIOs Leading Responsible AI Development Across Government
Since the White House's AI executive order, federal agencies are in the process of naming chief artificial intelligence officers.
7m read




