Cybersecurity
-

A Prepared Workforce is Key to Cyber Resiliency
2m read -

Coast Guard Poised for Growth in Cyber
23m listen
Energy Researchers Aim For Holistic Approach to AI Issues
A new center at the Oak Ridge National Laboratory is looking at under-researched areas of AI to better understand how to secure it.

This is a carousel with manually rotating slides. Use Next and Previous buttons to navigate or jump to a slide with the slide dots
-

Sea-Air-Space: Marine Innovation Unit Bridges Defense and Commercial Tech
Commanding Officer Col. Brooks Braden said the office is focused on how to innovate using available resources in the Marine Corps.
10m watch -
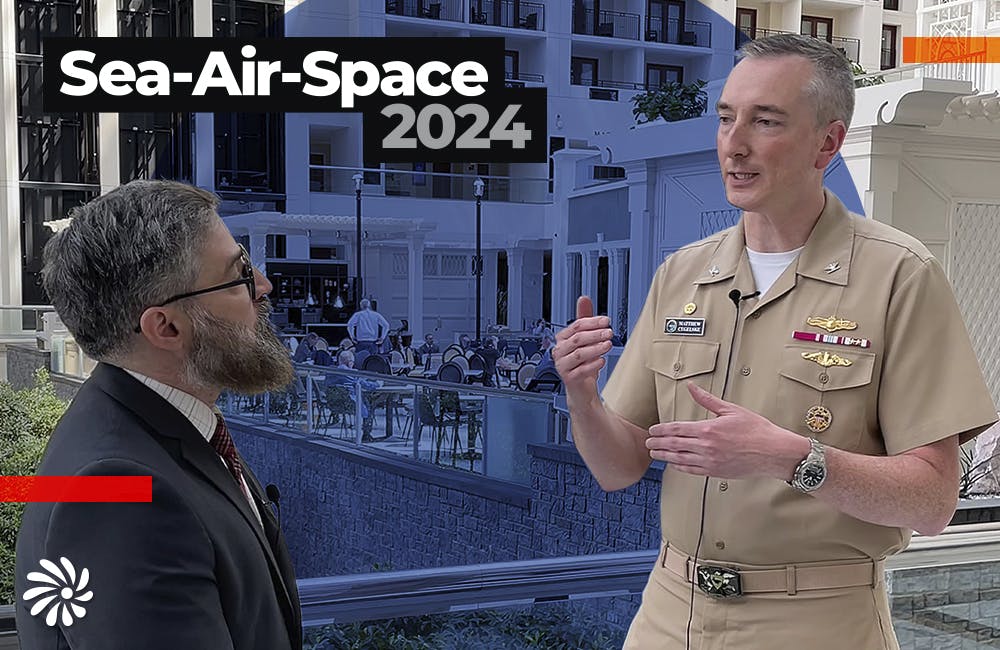
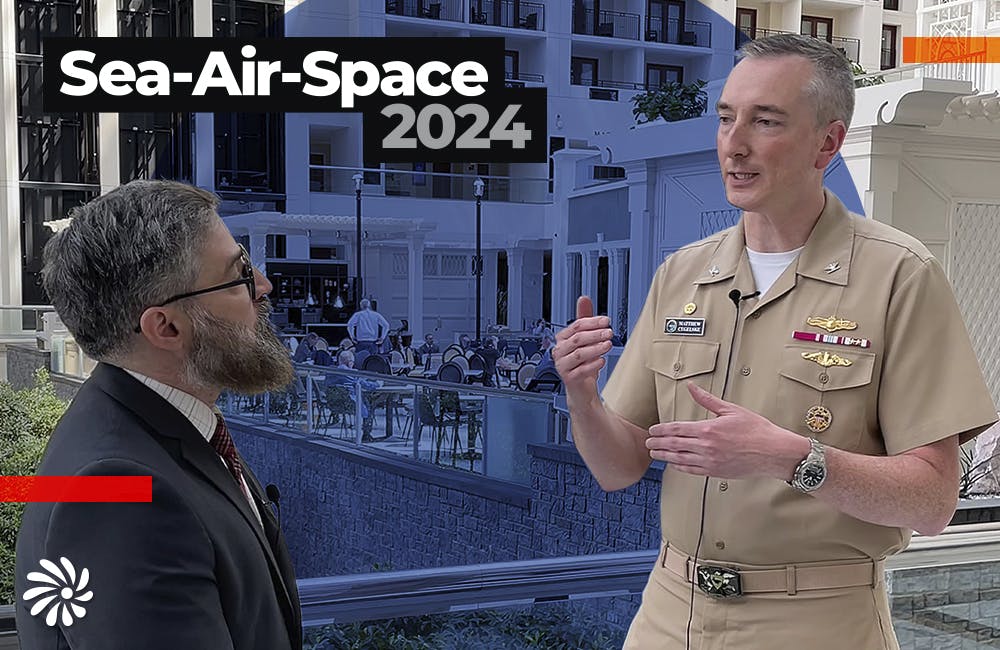
Sea-Air-Space: How Navy’s Intel Information Center is Keeping Data Safe
Hopper Global Communications Center Commanding Officer Captain Matt Cegelske says that security and usability can be balanced when accessing sensitive information.
9m watch -

Defense Officials: Cyber is a Sport That Needs Strong Teammates
Coast Guard, Marine Corps and Navy officials said they are working on new hiring strategies and partnerships amid evolving threats.
5m read -

Sea-Air-Space: Zero Trust is ‘The Best Approach’ For Military Cybersecurity
Marines Cyber Technology Officer Shery Thomas discusses identity management across networks and devices.
10m watch

How Agencies are Adjusting to the National Cyber Strategy
Hear from cyber leaders from EPA and Check Point Software Technologies about the future of cybersecurity as they adapt to new strategies and the changing cyber environment to meet the mission.
Watch Now- Tonya Manning CISO, EPA
- Pete Nicoletti Field CISO, Check Point Software Technologies
The Cybersecurity Talent Gap Peak Challenge for the Government
Digital Corps Fellow Brittney Wright uses her passion for cybersecurity to motivate the next generation of technologists.
Listen Now
-

Building Better Data Governance Across FDA
The agency is using emerging technology to tackle its data challenges.
19m listen -

Coast Guard Poised for Growth in Cyber
The service’s prevention policy chief discusses his priorities for combatting cyber incidents that could have global impacts.
23m listen -

How VA is Using Digital Services to Expand Care to Veterans
CIO Kurt DelBene says the the agency’s 2024 priorities included AI adoption, hiring and a better user experience for veterans.
30m listen -

Cancer HealthCast: This Unique Network Closes Research Gaps in Cancer Genomics
In this episode, Dr. Leah Mechanic, Program Director at NCI and Dr. Bettina Drake, Professor at Washington University School of Medicine
24m listen