Cyber Leaders Embrace New Draft Zero Trust Guidance
Agency leaders are pushing forth on security strategies for zero trust architecture amid new guidance.

The Office of Management and Budget and Cybersecurity and Infrastructure Security Agency just released new draft zero trust and cybersecurity guidance this week that will usher agencies toward adoption of modern security practices and architecture.
But how are various agencies’ security leadership responding the new guidance and recent cybersecurity executive orders, and how does the guidance align with their priorities?
As it turns out, federal cybersecurity officials are overall quite on board with the cybersecurity directives and guidance that are rolling out. The guidance aligns with many of these leaders’ goals and are normalizing a culture in their agencies that embraces cybersecurity.
The Federal Energy Regulation Committee, for instance, is embracing recent top-level cyber guidance and requirements. FERC CIO Mittal Desai said during an AFCEA event that the measures have been critical to encourage the modernization and cyber work that IT leadership has been trying to adopt, especially amid major cybersecurity incidents this past year like the SolarWinds hack.
More specifically, the FERC is about to undergo an application modernization multi-year effort. Desai added that the new cybersecurity directives are helping reinforce security into the change that modernization will bring to the agency.
“This is timely because as we’re about to kick this journey off, these architectural requirements have to be heavily considered,” Desai said. “Just talking with my security team this morning when this came out, they were very, very enthusiastic in respect to how we’re going to implement those goals.”
U.S. Citizenship and Immigration Services is more mature than the FERC in its IT infrastructure, as most of it is in the cloud, but USCIS CISO Shane Barney still said that the new OMB guidance will help recenter zero trust architecture in IT conversations.
“What I appreciate most about the OMB guidance template … is that it pulls us back into more of an architectural discussion,” Barney said. “It’s really driving us toward understanding best what our enterprise looks like, what we understand and define trust to be, what we consider important within our enterprise, and ultimately forcing us to recognize that the end-state goal of a zero-trust model is to place your entire enterprise on the public internet. That is the goal.”
The zero trust adoption that the OMB guidance reinforces also aligns with cybersecurity goals that the Department of Health and Human Services is trying to implement. HHS Cybersecurity Operations Deputy Director TJ Richardson mentioned that her organization has to coordinate enterprise visibility and cybersecurity across the various HHS agencies, such as the Centers for Disease Control and Prevention, Food and Drug Administration, and the National Institutes of Health.
These agencies within HHS each have different levels of zero trust adoption, so the guidance template and other measures Richardson is taking can help improve the coordinated cybersecurity activities across HHS’s agencies.
“HHS has been at the forefront in working with zero trust model,” Richardson said. “CDC has already done some things to implement and pilot, as well as the FDA, as well as NIH and some of the larger organizations, and we are always working with them to help coordinate.”
Richardson added that as HHS continues to coordinate zero trust cybersecurity practices and policies across its agencies, centralized logging and visibility will move forward as areas HHS wants to work on as well.
While larger agencies like HHS and USCIS look forward to the OMB guidance and requirements within the executive order, smaller agencies are, too. However, smaller agencies often lack the resources that larger agencies have to modernize their IT and meet cybersecurity requirements. National Archives and Records Administration Deputy CIO Sheena Burrell said that while the policy guidance and directives around zero trust and cybersecurity are exciting, there are some challenges that NARA faces to meet new cyber requirements.
“All aspects of the executive order and the recent policy are steps in the right direction,” Burrell said. “We’re continuing to see ransomware, and with each ransomware we’re seeing they’re building the ability to just do more bad things and their operational technology threats. I think these challenges are bad, especially for us because the budget cycle and the executive order did not align. … So while agencies are working on their 2023 budget submissions, the need to address these executive orders right now — we and some agencies like myself — we don’t have the resources to be able to actually execute on them.”
Although small agencies like NARA face budget challenges in meeting the needs of the executive order and zero trust guidance, Burrell said that she’s looking to tap the Technology Modernization Fund to help her agency bolster its cybersecurity to establish a zero-trust architecture.
“[We’re] looking at our high-value assets, or HVAs, trying to modernize those systems, as well as looking at our zero-trust architecture … and putting in a request for that Technology Modernization Fund because we didn’t have that money and we didn’t have those resources when these things came out,” Burrell said. “It is essential that people use [the TMF] as a starting point. … We don’t have the resources to be able to kind of drum up this zero-trust architecture overnight.”
While Burrell and other federal cybersecurity and IT leaders overall embrace the zero-trust draft guidance, it is open for public comment until Oct. 1.
This is a carousel with manually rotating slides. Use Next and Previous buttons to navigate or jump to a slide with the slide dots
-

Sea-Air-Space: Zero Trust is ‘The Best Approach’ For Military Cybersecurity
Marines Cyber Technology Officer Shery Thomas discusses identity management across networks and devices.
10m watch -

How Agencies are Justifying Budget Growth in AI, Zero Trust
IT leaders stressed the importance of understanding user knowledge and needs when prioritizing cybersecurity projects.
3m read -

DOJ Weighs 'Bring Your Own Devices' Amid Increased Threats
The agency wants stronger industry standards around cybersecurity before considering a more tailored mobile device policy.
2m read -
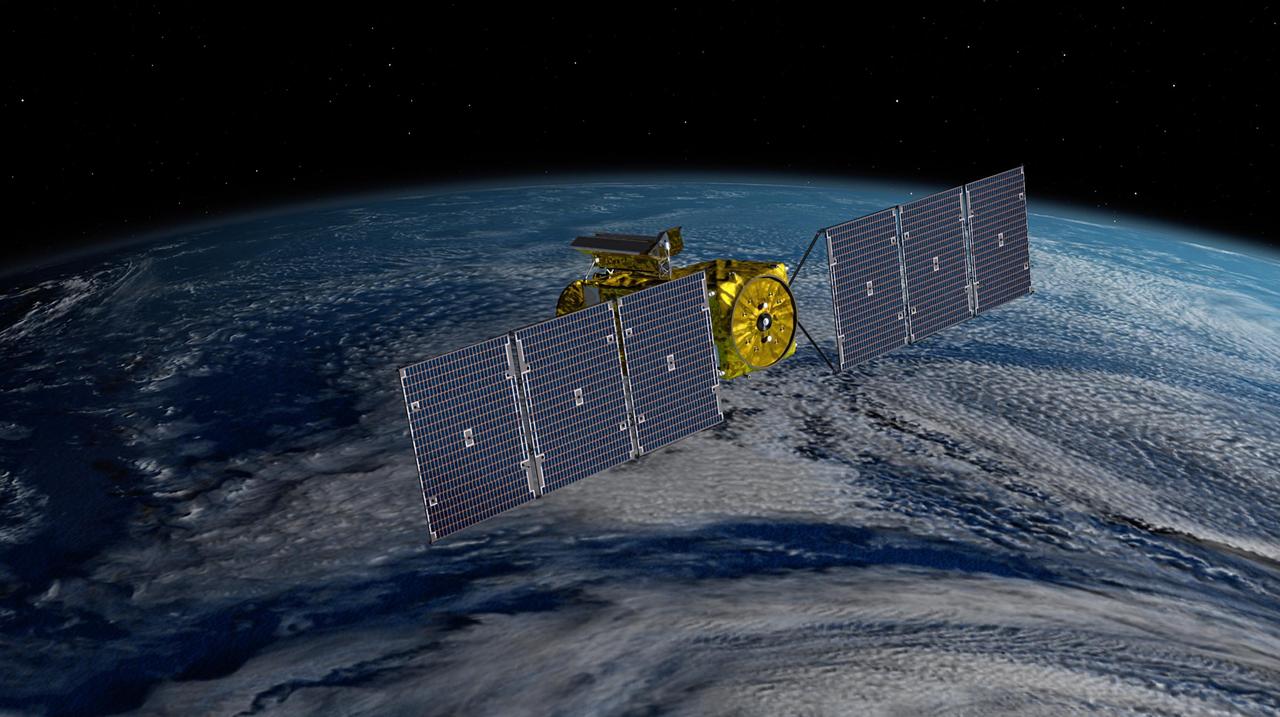
Officials Consider Zero Trust Challenges for Satellite Cybersecurity
Infrastructure experts call for better public-private cooperation to tackle cybersecurity in the planet's orbit.
4m read




